Last Updated: February 2026
Quick Answer
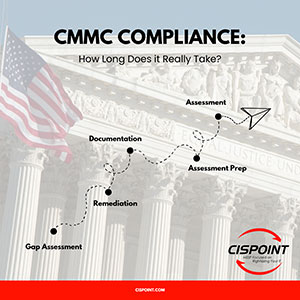
CMMC Level 1 typically takes 2-4 months from start to self-assessment completion. CMMC Level 2 requires 6-12 months for most organizations, though complex environments may need 12-18 months. The timeline depends heavily on your current security posture, organizational size, technical complexity, and resource availability. Starting immediately is critical - DoD contracts are beginning to require CMMC certification, and enforcement penalties for non-compliance include contract loss and potential False Claims Act liability.
| Timeline Factor | Level 1 | Level 2 |
|---|---|---|
| Typical Duration | 2-4 months | 6-12 months |
| Gap Assessment | 1-2 weeks | 2-4 weeks |
| Remediation | 1-2 months | 4-8 months |
| Documentation | 2-4 weeks | 2-3 months |
| Assessment Preparation | 2 weeks | 1-2 months |
| Assessment | Self-assessment (1 day) | C3PAO assessment (3-5 days) |
| Common Extensions | Minimal delays | Technology procurement, budget cycles |
Table of Contents
- Understanding CMMC Timeline Realities
- CMMC Level 1 Timeline Breakdown
- CMMC Level 2 Timeline Breakdown
- CMMC Implementation Deadlines and Enforcement
- Where to Start Your CMMC Journey
- What Delays CMMC Projects
- How to Accelerate Your Timeline
- Timeline Planning Tool: Your Implementation Checklist
- Enforcement Timeline and Penalties
- Real-World Timeline Examples
Understanding CMMC Timeline Realities
 The question "how long does CMMC take?" doesn't have a single answer because compliance isn't a linear process with a fixed duration. Your timeline depends on where you're starting, where you need to go, and what obstacles you'll encounter along the way.
The question "how long does CMMC take?" doesn't have a single answer because compliance isn't a linear process with a fixed duration. Your timeline depends on where you're starting, where you need to go, and what obstacles you'll encounter along the way.
The Starting Point Matters Most
An organization that already has robust cybersecurity practices, comprehensive documentation, and mature IT infrastructure will move through CMMC implementation far faster than one starting from basic security or outdated systems.
A defense contractor in Columbia, Maryland that's been following NIST SP 800-171 guidance for several years might complete Level 2 certification in 6 months. A similar-sized contractor in the same area that's been operating with minimal security controls could need 15 months for the same certification.
The gap between your current state and CMMC requirements drives your timeline more than any other factor. This is why the first step - the gap assessment - is so critical. It provides the roadmap for everything that follows.
Organizational Factors That Impact Timeline
Company Size and Complexity: A 10-person engineering firm with a simple IT environment will move faster than a 200-person manufacturer with multiple locations, legacy systems, and complex network architecture. More systems mean more controls to implement, more documentation to create, and more personnel to train.
Resource Availability: Organizations that can dedicate internal staff to CMMC implementation full-time progress faster than those where compliance work competes with operational responsibilities. Budget constraints that delay technology purchases or consulting engagements extend timelines significantly.
Technical Debt: Years of accumulated IT decisions - outdated software, unmanaged systems, poorly documented networks - create remediation work that extends timelines. Cleaning up technical debt isn't optional for CMMC; it's prerequisite work that must be completed before you can implement required controls.
Decision-Making Speed: Organizations with streamlined approval processes for technology purchases, policy changes, and security initiatives move faster than those with complex approval chains or hesitant leadership. Every week spent debating whether to implement multi-factor authentication is a week added to your timeline.
External Dependencies: If you rely on third-party IT providers, cloud services, or managed security services, your timeline depends partly on their responsiveness and capabilities. Switching providers or upgrading services adds weeks or months to implementation.
The Myth of the "Crash Program"
Some organizations, facing contract deadlines or new CMMC requirements, attempt to compress implementation into unrealistic timeframes. This rarely works and often backfires.
CMMC implementation requires thoughtful design, careful documentation, thorough testing, and meaningful integration into operations. Rushing produces incomplete implementations, inadequate documentation, and poorly trained staff - all of which result in failed assessments.
A failed C3PAO assessment doesn't just cost the assessment fee (typically $15,000-$75,000). It means you cannot bid on or receive contracts requiring your certification level until you remediate deficiencies and pass a new assessment. The delay can be 3-6 months, plus the cost and disruption of a second assessment.
Starting early and planning realistic timelines produces better outcomes than scrambling to meet impossible deadlines.
CMMC Level 1 Timeline Breakdown
Level 1 implementation follows a more straightforward path than Level 2, but don't mistake "simpler" for "easy." The 17 required practices still demand careful implementation and documentation.
Month 1: Assessment and Planning
Weeks 1-2: Gap Assessment
Your Level 1 journey begins with understanding where you currently stand against the 17 required practices. This gap assessment can be conducted internally or with consultant support.
The assessment examines each practice in detail. For access control, do you actually limit system access to authorized users? Do employees have individual accounts, or are you sharing credentials? When someone leaves the organization, is their access promptly removed?
For media protection, what happens to old hard drives and USB devices? Do you have documented procedures for sanitizing them before disposal, or have you been throwing equipment away without ensuring data is unrecoverable?
The gap assessment produces a findings document identifying which practices you've already implemented, which need enhancement, and which are completely absent. This becomes your implementation roadmap.
Weeks 3-4: Planning and Prioritization
With gap assessment findings in hand, you develop an implementation plan. Some findings require immediate attention - critical security gaps that create serious vulnerabilities. Others can be addressed in logical sequence.
You identify what resources you'll need. Will you implement controls with internal staff, or do you need external consultants? What technology purchases are required? Who needs to be involved in policy development and approval?
Budget allocation happens during this phase. Even Level 1 has costs - potentially new firewall equipment, endpoint protection software, documentation tools, and training materials. Getting budget approval now prevents delays later.
Month 2: Implementation
Weeks 5-8: Control Implementation
This is where the actual work happens. You're implementing the security controls identified as gaps in your assessment.
Access control implementation might mean creating individual user accounts to replace shared credentials, implementing a process for provisioning access when new employees start, and establishing procedures for removing access when they leave.
Physical protection could involve installing locks on server closets, implementing visitor sign-in procedures, and ensuring workstations in common areas have privacy screens or are positioned to prevent unauthorized viewing.
System and communications protection typically means configuring firewalls properly, ensuring guest Wi-Fi is separated from business networks, and documenting how external connections are managed.
Media protection requires developing and documenting procedures for sanitizing storage devices before disposal, maintaining records of sanitization activities, and training staff on proper procedures.
This phase takes the longest because it involves actual changes to how your organization operates. Technology implementations, policy development, and procedure changes all compete with daily operational demands.
Month 3: Documentation and Training
Weeks 9-10: Policy and Procedure Documentation
CMMC requires documentation of your security practices. For Level 1, this doesn't need to be as extensive as Level 2's System Security Plan, but you need clear, written policies and procedures covering each of the 17 practices.
Documentation describes what you do, how you do it, and who's responsible. It provides evidence of implementation and serves as training material for staff.
Good documentation is specific without being overly complex. "We limit system access to authorized users by requiring individual accounts for each employee, conducting quarterly access reviews, and removing access within 24 hours of termination" is clear and verifiable.
Weeks 11-12: Staff Training and Internal Review
All personnel need to understand their security responsibilities. Training covers relevant policies and procedures, how to recognize security threats, and what to do if they suspect a security incident.
You also conduct an internal review of your implementations. Are controls working as intended? Is documentation accurate and complete? Are there any lingering gaps that need attention before attestation?
Month 4: Attestation and Finalization
Weeks 13-14: Self-Assessment Execution
For Level 1, you conduct your own assessment of compliance with the 17 practices. This means systematically reviewing each practice, verifying implementation, and documenting compliance.
The self-assessment should be thorough and honest. If a practice isn't fully implemented, attest to that and document your plan for remediation. False attestation creates legal and contractual liability.
Weeks 15-16: Attestation Submission and Ongoing Maintenance
You submit your annual attestation of compliance through the Supplier Performance Risk System (SPRS) or whatever system the DoD implements for CMMC attestations.
With attestation complete, you shift to maintenance mode - keeping controls operational, updating documentation as things change, and preparing for next year's attestation.
What Can Accelerate Level 1 Timeline?
Strong Starting Position: Organizations that already follow basic security practices can complete Level 1 in 6-8 weeks rather than 3-4 months.
Dedicated Resources: Assigning someone to focus on CMMC implementation rather than fitting it between other responsibilities speeds progress significantly.
Pre-Existing Documentation: If you have documented IT policies and procedures, adapting them for CMMC is faster than creating documentation from scratch.
Simple IT Environment: Smaller organizations with straightforward IT setups have less complexity to address, shortening implementation time.
What Commonly Delays Level 1 Projects?
Budget Approval Processes: Waiting weeks or months for approval to purchase required technology extends timelines unnecessarily.
Lack of Internal Expertise: Organizations without IT security knowledge struggle to interpret requirements and design appropriate implementations.
Competing Priorities: When CMMC work competes with operational demands and loses, implementation stalls.
Scope Creep: Attempting to implement comprehensive security beyond Level 1 requirements delays completion without adding certification value.
CMMC Level 2 Timeline Breakdown
Level 2 represents a substantial undertaking that touches every aspect of your IT environment and business operations. The 110 practices from NIST SP 800-171 create a comprehensive security framework requiring significant time to implement properly.
Months 1-2: Assessment and Planning
Weeks 1-3: Comprehensive Gap Assessment
Level 2 gap assessment is far more involved than Level 1. You're evaluating 110 practices across 14 security domains, examining technical implementations, documentation, policies, and operational processes.
A qualified Registered Practitioner Organization (RPO) typically conducts this assessment, bringing expertise in interpreting NIST SP 800-171 requirements and identifying compliant implementation approaches.
The assessment examines your entire IT infrastructure. Network architecture, system configurations, access controls, encryption implementations, logging and monitoring capabilities, incident response procedures, physical security, personnel security, and much more.
For each of the 110 practices, the assessment determines whether you're compliant, partially compliant, or non-compliant. Partially compliant means you have some elements in place but gaps remain. Non-compliant means the practice isn't implemented at all.
The gap assessment produces a detailed findings report, typically 30-50 pages, documenting current state, required future state, and specific recommendations for achieving compliance.
Weeks 4-8: Strategic Planning and Scoping
With gap findings in hand, you develop a comprehensive implementation plan. This involves critical decisions about your approach to CMMC compliance.
Scoping decisions are particularly important. Will you implement Level 2 controls across your entire IT environment, or will you create a CMMC-compliant enclave for CUI and keep general business systems separate?
Enclave strategies can reduce costs but create operational complexity. You need strict boundaries between the enclave and the rest of your network, processes to prevent CUI from leaking into unprotected systems, and disciplined information handling by all personnel.
Resource allocation happens during planning. Will you use internal resources, external consultants, or a combination? What's the budget for technology purchases? Who will lead the implementation? How much time can key personnel dedicate to CMMC work?
Technology roadmap development identifies what systems need to be purchased, upgraded, or replaced. Multi-factor authentication solutions, encryption tools, logging and monitoring platforms, backup systems, and potentially entire infrastructure replacements.
Timeline and milestone planning creates a realistic schedule with specific deliverables. Which practices will you tackle first? What's the critical path? Where are dependencies that could delay progress?
Months 3-6: Core Implementation
Months 3-4: Critical Security Control Implementation
Implementation begins with the most critical security controls and those with long lead times.
Multi-factor authentication (MFA) deployment typically happens early because it's a clear requirement and foundational to access security. You select an MFA solution, deploy it to all systems, enroll all users, and establish procedures for MFA management.
Encryption implementation for data at rest and in transit often involves significant technical work. You may need to migrate to encrypted storage systems, implement VPN solutions for remote access, configure encrypted email, and ensure all CUI is stored in encrypted repositories.
Network segmentation to separate CUI systems from general business networks requires careful network design, potentially new firewall equipment, VLAN configuration, and extensive testing to ensure segmentation is effective without disrupting operations.
Logging and monitoring capabilities need to be established if they don't exist or enhanced if current capabilities are inadequate. This means deploying log collection systems, configuring systems to generate appropriate logs, establishing log review processes, and potentially implementing SIEM (Security Information and Event Management) solutions.
These core implementations often have procurement lead times. Ordering hardware, waiting for delivery, scheduling installations, and completing configurations can take weeks or months.
Months 5-6: Comprehensive Practice Implementation
With foundational controls in place, implementation expands to cover all 110 practices across all 14 domains.
Access control practices require implementing role-based access, least privilege principles, privileged account management, session controls, and remote access protections.
Configuration management means establishing baseline configurations, implementing change control processes, restricting software installations, and monitoring for unauthorized changes.
Incident response requires developing a formal incident response plan, establishing an incident response capability, implementing incident tracking, and conducting plan testing.
Media protection involves comprehensive controls for media access, transport, sanitization, and accountability.
Each domain has multiple practices, each practice requires thoughtful implementation, and everything must work together as a coherent security program.
Months 7-8: Documentation Development
Month 7: System Security Plan (SSP) Development
The SSP is the comprehensive document describing your entire security implementation. It details your IT environment, explains how you implement each of the 110 practices, provides evidence of implementation, and documents any planned remediations.
SSP development is intensive work. You're documenting network architecture, system inventories, security control implementations, policies and procedures, and operational processes. The SSP typically runs 100-200 pages depending on organizational complexity.
Good SSP development requires technical expertise to accurately describe implementations and writing skill to create clear, organized documentation that assessors can follow.
Month 8: Supporting Documentation
Beyond the SSP, you need extensive supporting documentation including detailed policies and procedures for each security domain, network diagrams, asset inventories, configuration baselines, incident response plans, training materials, and evidence of practice implementation.
Plan of Action and Milestones (POA&M) documentation is developed for any practices that aren't yet fully implemented but will be completed before assessment.
Months 9-10: Testing and Refinement
Month 9: Internal Security Testing
Before inviting a C3PAO to assess your environment, you need confidence that everything works as documented. Internal testing validates technical control implementations, verifies documentation accuracy, and identifies remaining gaps.
Testing includes vulnerability scanning, penetration testing, configuration reviews, access control verification, encryption validation, and logging and monitoring verification.
Testing often reveals issues - controls that aren't quite right, documentation that doesn't match reality, or gaps that were overlooked during implementation. Remediation of these findings happens during this phase.
Month 10: Staff Training and Preparation
All personnel need comprehensive security awareness training covering CMMC requirements, your specific security policies and procedures, threat recognition, and incident reporting.
Personnel who will interact with assessors during the C3PAO assessment need specific preparation. They should understand their roles in security, be able to articulate how practices are implemented, and know where to find supporting evidence.
Practice interviews help staff become comfortable discussing security practices with assessors and ensure consistent, accurate responses.
Months 11-12: Assessment Preparation and Execution
Month 11: Pre-Assessment Readiness Review
A final comprehensive review ensures everything is ready for the C3PAO assessment. This includes reviewing all documentation for completeness and accuracy, verifying all 110 practices are fully implemented, confirming evidence is available and organized, ensuring staff are prepared, and resolving any remaining issues.
Many organizations engage their RPO to conduct a pre-assessment review simulating the actual C3PAO assessment. This identifies any remaining issues before the formal assessment when they can still be fixed.
Month 12: C3PAO Assessment
You engage a certified C3PAO to conduct your formal assessment. Assessment scheduling often requires 2-3 months lead time due to C3PAO availability, so you typically schedule this during earlier phases of implementation.
The assessment event itself takes 3-5 days for most organizations, during which assessors review documentation, interview personnel, test technical controls, and validate practice implementation.
Following the assessment, you receive a report indicating which practices are compliant and which have findings. Any practice with findings results in assessment failure - there's no partial certification. You must remediate all findings and potentially undergo re-assessment.
Upon successful assessment, you receive CMMC Level 2 certification valid for three years.
What Can Accelerate Level 2 Timeline?
Strong NIST SP 800-171 Foundation: Organizations that have already implemented many NIST SP 800-171 practices can complete Level 2 in 4-6 months rather than 6-12 months.
Modern IT Infrastructure: Current systems, cloud-based infrastructure, and recent technology reduce the technical debt that slows implementation.
Dedicated Project Team: Having internal resources focused exclusively on CMMC implementation rather than balancing it with other responsibilities significantly accelerates progress.
Executive Support and Quick Decisions: Strong leadership backing and streamlined approval processes eliminate delays caused by decision paralysis or budget battles.
Experienced RPO Partnership: Working with an RPO that knows CMMC intimately prevents time wasted on wrong approaches or rework.
Available Budget: Having financial resources ready to purchase necessary technology without lengthy procurement processes keeps implementation moving.
What Commonly Delays Level 2 Projects?
Underestimating Scope: Organizations that expect Level 2 to be moderately more complex than Level 1 discover it's an order of magnitude more involved.
Technology Procurement Lead Times: Waiting months for equipment delivery, software licensing, or cloud service provisioning stalls implementation.
Resource Constraints: Attempting Level 2 with inadequate internal resources or insufficient consulting support stretches timelines indefinitely.
Scope Changes Mid-Project: Deciding to expand CMMC scope, change enclave strategies, or implement controls differently requires rework that adds months.
Documentation Challenges: Organizations without strong technical writing capabilities struggle to create the SSP and supporting documentation, causing extensive delays.
Staff Resistance: Implementing new security controls that change how people work creates resistance that slows adoption and implementation.
Assessment Scheduling: C3PAO availability can push your assessment date months beyond when you're ready, extending the overall timeline.
CMMC Implementation Deadlines and Enforcement
Understanding the timeline for CMMC implementation isn't just about how long it takes your organization - it's also about when the DoD requires certification for contract eligibility.
The CMMC Rollout Timeline
CMMC 2.0 has been in development and refinement since 2021, but the mandatory implementation for DoD contracts has followed a phased approach.
2024-2025: Pilot Phase and Initial Implementation
During 2024 and into 2025, CMMC requirements began appearing in select DoD contracts as the program moved from voluntary to mandatory status. High-priority programs and contracts involving sensitive CUI were first to include CMMC requirements.
This pilot phase allowed the DoD to refine processes, C3PAOs to gain assessment experience, and the defense industrial base to begin preparation without sudden universal requirements.
2026: Accelerating Requirements
Throughout 2026, CMMC requirements are appearing in an increasing number of DoD contracts and task orders. The DoD is implementing CMMC across different contract types and program offices in waves rather than all at once.
Current DoD guidance indicates that by late 2026, a substantial portion of new DoD contracts will require CMMC certification appropriate to the information handled under the contract.
2027 and Beyond: Universal Implementation
By 2027, the expectation is that CMMC will be a standard requirement in DoD contracts involving FCI or CUI. Contracts without CMMC requirements will be the exception rather than the rule.
Contract-Specific Timelines
Your specific deadline depends on your contracts and customers. If you're currently working only on contracts awarded before CMMC requirements were implemented, you may have some breathing room. But several scenarios create urgency:
New Contract Pursuits: If you want to bid on new DoD contracts that include CMMC requirements, you must have appropriate certification before you can be considered for award.
Contract Renewals and Modifications: Existing contracts may incorporate CMMC requirements upon renewal or modification. Your contract that didn't require CMMC when awarded in 2023 may require it when renewed in 2026.
Subcontractor Flow-Down: If you're a subcontractor and your prime is required to have CMMC certification, they will flow that requirement down to you. You must achieve certification within the timeframe specified by the prime.
Customer-Driven Timelines: Some government customers and prime contractors are requiring CMMC certification earlier than mandatory deadlines as a risk mitigation measure.
What Happens If You Miss Deadlines?
The consequences of not having required CMMC certification when contracts mandate it are severe and immediate.
Contract Ineligibility: You cannot bid on or receive awards for contracts requiring CMMC certification if you don't have the appropriate level. This isn't a soft deadline - it's a hard eligibility requirement.
Loss of Existing Contracts: Contracts that incorporate CMMC requirements through modification or renewal cannot continue if you don't achieve required certification. You lose the work.
Subcontractor Replacement: Prime contractors cannot flow CUI to subcontractors without appropriate CMMC certification. If you don't certify, the prime must replace you with a certified subcontractor.
No Grace Periods: Unlike some compliance requirements where you might get warnings or grace periods to remediate issues, CMMC certification is binary. You either have it or you don't. Without it, you're ineligible.
CMMC Enforcement and Penalties
Beyond contract ineligibility, failure to meet CMMC requirements creates additional risks.
DFARS 252.204-7012 Violations: Most organizations pursuing CMMC are already subject to DFARS 252.204-7012, which requires implementation of NIST SP 800-171 practices (essentially Level 2 controls). If you have this contract clause but haven't implemented required controls, you're already in violation of contract terms.
False Claims Act Exposure: If you've attested to compliance with DFARS 252.204-7012 but haven't actually implemented required practices, you could face False Claims Act liability. False Claims Act violations carry penalties of $13,946 to $27,894 per false claim, plus potential treble damages.
Breach Notification and Reporting Requirements: If you're required to protect CUI but haven't implemented adequate controls, and CUI is compromised in a breach, you face reporting obligations to DoD, potential investigation, and liability for the breach.
Cybersecurity Maturity Model Certification Accountability: The CMMC framework includes provisions for verifying ongoing compliance and investigating potential violations. Organizations that receive CMMC certification but fail to maintain compliance can have certification revoked and face contract consequences.
Reputation and Business Impact: Beyond formal penalties, failure to achieve or maintain CMMC certification damages your reputation in the defense market. Primes may be reluctant to work with contractors who have compliance issues, and you may lose competitive opportunities even for contracts that don't explicitly require CMMC.
The Cost of Delay
Every month you delay starting CMMC implementation increases your risk of missing critical contract deadlines. Consider these scenarios:
Scenario 1: Maryland Defense Contractor
A 50-person engineering firm in Columbia, Maryland has several DoD contracts set to renew in July 2026. All renewals will require CMMC Level 2 certification. They began implementation in January 2026, giving themselves 6 months.
Month 3 revealed that their legacy systems couldn't support required encryption, necessitating infrastructure replacement with 8-week lead time. They're now looking at completing implementation in August - after their contract renewal dates.
They face losing $2.3 million in annual contract revenue because they started 2-3 months too late to accommodate unexpected delays.
Scenario 2: Small Manufacturer
A 15-person precision manufacturing company in Huntsville, Alabama assumed their work didn't involve CUI because final products are unclassified. In March 2026, their prime contractor notified them that technical drawings and specifications they receive constitute CUI, requiring Level 2 certification by June for continued subcontract work.
Three months is insufficient for proper Level 2 implementation. They face choosing between attempting a rushed, incomplete implementation likely to fail assessment, or losing their largest customer and 60% of annual revenue.
Scenario 3: Proactive Preparation
A systems engineering firm in Northern Virginia began CMMC Level 2 implementation in January 2025, before any of their contracts required it. They completed certification in July 2025.
When their major contract renewed in March 2026 with CMMC requirements, they were already certified. When they bid on a high-priority program in May 2026, their existing certification gave them a competitive advantage over bidders still working toward compliance.
The lesson is clear: starting early provides buffer for unexpected complications and positions you for competitive advantage.
Where to Start Your CMMC Journey
Understanding that CMMC takes months to complete, and that deadlines are approaching, raises the urgent question: where do you begin?
First 30 Days: Critical Actions
Days 1-7: Determine Your CMMC Level Requirement
Before you can plan implementation, you must know whether you need Level 1 or Level 2 certification. This requires careful analysis of your contracts, the information you handle, and your role in the defense supply chain.
Review all current DoD contracts and subcontracts for CMMC requirements, DFARS 252.204-7012 clauses, and references to CUI protection. Examine the type of information flowing to your organization from government customers or primes.
If you handle technical data, specifications, source code, test results, operational information, or any CUI category, you need Level 2. If you only handle basic contract information like invoicing and schedules, Level 1 may suffice.
When uncertain, consult with your contracting officer, prime contractors, or engage a CMMC consultant for a definitive determination. Choosing the wrong level wastes time and money.
Days 8-14: Assess Your Current Security Posture
Even before conducting a formal gap assessment, you can evaluate your starting point by asking basic questions:
Do users have individual accounts, or are credentials shared? Is multi-factor authentication implemented? Are systems patched regularly? Do you have documented security policies? Is sensitive data encrypted? Are logs reviewed? Is there an incident response plan?
Honest answers to these questions reveal whether you're starting from a strong security foundation or basic practices. This rough assessment helps you understand the magnitude of work ahead.
Days 15-21: Assemble Resources and Assign Responsibility
CMMC implementation doesn't happen accidentally. Someone must drive the effort, coordinate activities, make decisions, and maintain momentum.
Designate a CMMC program manager or project lead with authority to move the initiative forward. This person needs dedicated time for CMMC work - it can't be an afterthought squeezed between other responsibilities.
Determine whether you'll implement with internal resources, external consultants, or a combination. For Level 2 particularly, most organizations benefit from experienced RPO guidance.
Secure executive support and budget allocation. CMMC requires financial investment for technology, consulting, assessment fees, and staff time. Getting leadership commitment now prevents budget battles later.
Days 22-30: Engage Professional Gap Assessment
For Level 2 particularly, engage a qualified RPO to conduct a comprehensive gap assessment. This assessment provides the roadmap for everything that follows and is money well spent.
The gap assessment should produce clear findings documenting your current state for each required practice, specific recommendations for achieving compliance, a preliminary cost estimate, and a realistic timeline estimate.
With gap assessment complete, you have the information needed to develop a detailed implementation plan, secure necessary budget, and begin the actual compliance work.
Common Starting Mistakes to Avoid
Attempting to Implement Without Understanding Requirements: Don't start buying technology or changing configurations before you understand what CMMC actually requires. Premature implementation often creates rework when you discover your approach doesn't meet requirements.
Underestimating Documentation Requirements: CMMC isn't just technical implementation - it requires extensive documentation. Organizations that focus solely on technology and ignore documentation face significant delays.
Trying to Do Everything Internally Without Expertise: CMMC is complex and nuanced. Organizations without cybersecurity expertise struggle to interpret requirements correctly and design compliant implementations. Engaging experienced consultants accelerates progress and improves outcomes.
Analysis Paralysis: Some organizations spend months researching, discussing, and planning without making concrete progress on implementation. Perfect plans are less valuable than good plans executed promptly.
Scope Creep: Attempting to implement comprehensive security far beyond CMMC requirements delays certification without adding certification value. Focus on meeting requirements first; additional security enhancements can come after certification.
What Delays CMMC Projects (And How to Avoid Them)
Understanding common delay factors helps you plan proactively to avoid them.
Technology Procurement Lead Times
The Problem: Ordering firewalls, servers, encryption solutions, or other equipment can involve weeks or months of lead time from order to delivery and installation. Cloud service provisioning may be faster but still involves procurement processes, contract negotiations, and implementation time.
The Impact: Organizations discover 3 months into implementation that required equipment has 8-week delivery times, pushing timeline completion by 2 months.
The Solution: Identify technology requirements early in your gap assessment and begin procurement processes immediately. Don't wait until you're "ready" to implement - order long-lead-time items as soon as you know you'll need them.
Budget Approval Processes
The Problem: Many organizations require multiple layers of approval for technology purchases, consulting engagements, and project expenditures. Budget cycles may only open annually or quarterly.
The Impact: Implementation stalls for weeks or months while waiting for budget approval that could have been obtained earlier with proper planning.
The Solution: Develop comprehensive budget requirements early based on gap assessment findings. Present leadership with clear cost justification tied to contract requirements and deadlines. Secure budget allocation before beginning implementation to prevent approval delays from disrupting progress.
Competing Organizational Priorities
The Problem: CMMC implementation competes with operational demands, customer deliverables, and other strategic initiatives. When CMMC loses prioritization battles, implementation slows or stalls.
The Impact: Progress is inconsistent, with bursts of activity followed by periods of inactention. Implementation that could complete in 6 focused months stretches to 12 or more.
The Solution: Executive leadership must establish CMMC as a strategic priority with clear deadlines and accountability. Dedicated resources should be assigned to CMMC work rather than expecting people to fit it in "when they have time."
Inadequate Internal Expertise
The Problem: Organizations attempt CMMC implementation without cybersecurity expertise, struggle to interpret requirements correctly, design implementations that don't meet requirements, and create documentation that doesn't adequately describe their security program.
The Impact: Rework cycles as incorrect approaches are abandoned and rebuilt. Assessment failures requiring remediation and re-assessment. Extended timelines due to learning curves.
The Solution: Engage experienced CMMC consultants or RPOs from the beginning. Their expertise accelerates progress, prevents costly mistakes, and produces implementations likely to pass assessment.
Documentation Challenges
The Problem: Many technically proficient organizations struggle with documentation. They implement security controls correctly but fail to document implementations adequately for assessment.
The Impact: Assessment delays while documentation is created or enhanced. Assessment failures due to inadequate documentation even when technical controls are properly implemented.
The Solution: Plan documentation effort from the beginning as equal priority to technical implementation. Assign people with strong writing skills to documentation development. Use templates and examples to accelerate creation.
Scope Changes Mid-Implementation
The Problem: Organizations discover new information during implementation that changes their understanding of requirements, decide to modify their scoping strategy, or identify additional contracts that need CMMC certification.
The Impact: Rework of completed items under the new approach. Extension of timeline to accommodate expanded scope. Potential delays to re-evaluate decisions and adapt plans.
The Solution: Invest heavily in upfront planning and scoping to get decisions right the first time. Once implementation begins, maintain scope discipline and defer scope changes to after certification unless absolutely necessary.
Assessment Scheduling Challenges
The Problem: C3PAOs have limited capacity and significant demand. Organizations ready for assessment may face 2-3 month wait times to schedule.
The Impact: Timeline extension waiting for assessment availability even though implementation is complete.
The Solution: Engage and schedule C3PAO early in your implementation timeline rather than waiting until you're ready. Most C3PAOs book assessments months in advance. Schedule your assessment for your target completion date during early implementation phases.
Staff Resistance and Change Management
The Problem: Security controls change how people work. Multi-factor authentication adds steps to login. Encryption may slow file access. New policies restrict previously permissible actions. Some staff resist changes and undermine implementation.
The Impact: Slow adoption of new security practices. Implementations that work technically but aren't used properly operationally. Cultural resistance that extends implementation timelines.
The Solution: Invest in change management and communication from the beginning. Explain why CMMC is necessary and how it protects the organization. Provide comprehensive training. Address concerns and resistance proactively. Secure leadership support to require compliance.
How to Accelerate Your Timeline (Realistically)
While CMMC implementation has inherent minimum timeframes, several approaches can compress timelines without sacrificing quality.
Start with Strong Executive Support
Organizations that have clear executive mandate for CMMC, visible leadership involvement, and quick decision-making on CMMC matters move faster than those where implementation is an IT department initiative with limited leadership engagement.
Executive support manifests as:
- Clear communication that CMMC is a strategic priority
- Rapid approval processes for CMMC-related expenditures
- Resources dedicated to CMMC work
- Accountability for CMMC milestones
- Removal of organizational barriers to implementation
This support eliminates delays caused by competing priorities, budget approval battles, and decision paralysis.
Engage Experienced Consultants Early
RPOs and CMMC consultants who have guided dozens or hundreds of organizations through implementation bring knowledge that prevents time-wasting mistakes.
They know which implementations work and which don't. They've seen the assessment process and know what assessors look for. They have templates, tools, and methodologies that accelerate progress.
The cost of consulting is far less than the cost of implementation delays, rework, or failed assessments. Organizations that engage consultants from the beginning typically complete implementation faster than those attempting to do it alone.
Implement in Focused Sprints
Rather than spreading CMMC work thinly over many months, consider intensive implementation sprints where dedicated teams focus exclusively on CMMC for defined periods.
A 2-week sprint focused exclusively on implementing multi-factor authentication across all systems accomplishes more than 3 months of part-time effort. Sprint-based approaches maintain momentum, reduce context-switching inefficiencies, and produce visible progress.
Leverage Modern Cloud Technologies
Organizations using modern cloud infrastructure (Microsoft 365 GCC High, AWS GovCloud, Azure Government) have many security controls built into their platforms. Encryption, logging, access controls, and other requirements are available as configuration options rather than requiring custom implementation.
Cloud-first approaches typically accelerate Level 2 implementation by 2-3 months compared to traditional on-premises infrastructure requiring custom security control implementation.
Standardize and Simplify
Complex IT environments take longer to secure than simple ones. Strategic simplification before CMMC implementation can significantly accelerate timelines.
Consolidating from multiple disparate tools to standardized platforms reduces the number of systems requiring security control implementation. Eliminating legacy systems that are difficult to secure removes barriers to compliance. Standardizing configurations makes implementation and documentation faster.
Use Templates and Frameworks
Don't reinvent every policy, procedure, and document from scratch. High-quality templates for SSPs, policies, procedures, and documentation exist. Experienced consultants provide templates tailored to your environment.
Adapting templates is far faster than creating documents from blank pages. Just ensure templates are actually customized to reflect your specific environment rather than left as generic boilerplate.
Parallel Path Implementation
Many CMMC practices can be implemented concurrently rather than sequentially. You can work on access controls while someone else develops policies while a third team implements encryption.
Careful project planning that identifies which activities can happen in parallel compresses timelines significantly. Just ensure parallel efforts are coordinated to avoid conflicting implementations.
Maintain Momentum
Implementation momentum matters. Organizations that make consistent progress week after week complete faster than those with sporadic bursts of activity separated by periods of inactivity.
Regular progress meetings, visible milestones, and accountability mechanisms help maintain momentum. Celebrate progress to keep teams engaged and motivated.
Timeline Planning Tool: Your Implementation Checklist
Use this checklist to plan and track your CMMC implementation timeline:
Pre-Implementation (Weeks 1-4)
☐ Determine CMMC level requirement (Level 1 or Level 2)
☐ Review all contracts for CMMC clauses and deadlines
☐ Identify information types handled (FCI vs CUI)
☐ Assign CMMC program manager/project lead
☐ Secure executive support and commitment
☐ Allocate preliminary budget
☐ Engage RPO for gap assessment (Level 2)
☐ Conduct internal readiness evaluation
Gap Assessment (Weeks 2-6)
☐ Complete formal gap assessment
☐ Review gap assessment findings with leadership
☐ Identify compliance gaps for each practice
☐ Develop remediation recommendations
☐ Estimate implementation costs
☐ Create preliminary timeline
☐ Secure final budget approval
Planning and Scoping (Weeks 5-8)
☐ Define CMMC assessment boundary/scope
☐ Make enclave vs full environment decision
☐ Develop detailed implementation plan
☐ Assign responsibilities for each practice
☐ Identify technology requirements
☐ Create procurement timeline
☐ Establish project milestones and schedule
☐ Engage C3PAO and schedule assessment (Level 2)
Implementation Phase (Months 2-8 for Level 2, Weeks 5-12 for Level 1)
☐ Procure required technology and services
☐ Implement access control practices
☐ Deploy multi-factor authentication (Level 2)
☐ Implement encryption for data at rest and in transit (Level 2)
☐ Configure network segmentation (Level 2)
☐ Establish logging and monitoring
☐ Deploy endpoint protection
☐ Implement physical security controls
☐ Establish incident response capability
☐ Implement configuration management
☐ Deploy media protection controls
☐ Implement all remaining practices
Documentation Phase (Overlapping with Implementation)
☐ Develop System Security Plan (Level 2)
☐ Create security policies and procedures
☐ Document network architecture
☐ Create asset inventory
☐ Develop incident response plan
☐ Create training materials
☐ Document evidence of practice implementation
☐ Create POA&M for any incomplete practices
Testing and Validation (Weeks/Months Before Assessment)
☐ Conduct internal security testing
☐ Perform vulnerability scanning
☐ Test access controls
☐ Verify encryption implementations
☐ Validate logging and monitoring
☐ Review documentation for accuracy and completeness
☐ Conduct pre-assessment readiness review
☐ Remediate findings from internal testing
Training and Preparation (Final Weeks)
☐ Conduct security awareness training for all personnel
☐ Train staff on CMMC-specific policies and procedures
☐ Prepare personnel for assessor interviews
☐ Organize evidence and documentation for assessment
☐ Final verification all practices implemented
☐ Leadership review and sign-off
Assessment (Final Phase)
☐ C3PAO assessment completion (Level 2, 3-5 days)
☐ Self-assessment completion (Level 1)
☐ Address any assessment findings
☐ Receive certification (Level 2)
☐ Submit attestation (Level 1)
☐ Update SPRS portal
Post-Certification
☐ Establish continuous compliance monitoring
☐ Schedule periodic internal reviews
☐ Maintain documentation
☐ Continue security awareness training
☐ Plan for recertification/re-attestation
Enforcement Timeline and Penalties
As CMMC transitions from voluntary to mandatory, understanding enforcement mechanisms and penalties is critical for timeline planning.
Current Enforcement Landscape (2026)
CMMC enforcement in 2026 is primarily contract-based. DoD contracts that include CMMC requirements make certification a condition of contract award and performance. You cannot bid on or receive these contracts without appropriate certification.
This creates clear, immediate consequences: no certification equals no contract eligibility. There's no need for separate enforcement mechanisms because contract ineligibility is the enforcement.
DFARS 252.204-7012 Penalties
While CMMC certification requirements are relatively new, most organizations subject to CMMC have been operating under DFARS 252.204-7012 for years. This clause requires implementation of NIST SP 800-171 practices (essentially Level 2 controls).
If you have this clause in contracts but haven't implemented required practices, you're already in violation. Penalties include:
Contract Breach: Failure to implement required security controls violates contract terms and can result in contract termination.
Withholding of Payments: DoD has authority to withhold payments from contractors not meeting DFARS 252.204-7012 requirements until compliance is achieved.
False Claims Act Liability: If you've represented compliance but haven't actually implemented controls, this could constitute false claims. Penalties range from $13,946 to $27,894 per false claim, plus treble damages.
Suspension and Debarment: Serious or repeated violations can result in suspension or debarment from government contracting.
Breach Reporting and Incident Penalties
DFARS 252.204-7012 includes breach reporting requirements. If CUI is compromised due to inadequate security controls, you must report the incident to DoD within 72 hours and conduct forensic analysis.
Breaches caused by failure to implement required security controls create additional liability beyond the breach itself. You've violated contract requirements, potentially exposed sensitive defense information, and may face investigation into your security practices.
The reputational damage from security breaches in the defense market can be more damaging than formal penalties. Primes become reluctant to share CUI with contractors who have suffered breaches, limiting future opportunities.
Timeline for Avoiding Penalties
The timeline to avoid CMMC-related penalties is simple: achieve required certification before contract requirements mandate it.
For contracts you currently hold, review renewal dates and anticipated modifications. If renewals or modifications will include CMMC requirements, ensure you have certification before those dates.
For new contract pursuits, ensure you have certification before bid submission for contracts that require it.
For subcontract work, comply with CMMC requirements within the timeframe specified by your prime contractor.
There are no extensions, waivers, or grace periods. The certification requirement is binary - you have it or you don't.
Real-World Timeline Examples
Seeing how actual organizations have navigated CMMC timelines provides practical perspective.
Example 1: Small Engineering Firm (Columbia, MD) - Level 2
Organization: 15-person systems engineering firm supporting DoD programs
Starting Point: Basic cybersecurity, limited documentation, some practices implemented
Timeline: 9 months from start to certification
Month 1: Gap assessment revealed 47 of 110 practices fully compliant, 38 partially compliant, 25 non-compliant. Major gaps in encryption, logging, network segmentation, and documentation.
Months 2-3: Implemented multi-factor authentication, deployed encryption for data at rest, began network segmentation project, upgraded firewall. Budget approval took 3 weeks longer than expected.
Months 4-6: Completed network segmentation, implemented comprehensive logging and SIEM, deployed additional access controls, developed incident response plan. Firewall delivery delay pushed some tasks by 3 weeks.
Months 7-8: SSP development, policy documentation, created supporting evidence packages. This took longer than planned - 10 weeks instead of expected 6.
Month 9: Internal readiness review, remediated final gaps, staff training, C3PAO assessment. Passed assessment with minor recommendations.
Key Success Factors: Strong executive support, engaged RPO from beginning, dedicated project manager, willingness to invest in necessary technology.
Challenges: Technology lead times, documentation more time-consuming than expected, staff vacation schedules complicated training coordination.
Example 2: Mid-Size Manufacturer (Huntsville, AL) - Level 2
Organization: 75-person precision manufacturing company
Starting Point: Outdated IT infrastructure, minimal cybersecurity beyond antivirus, no formal policies
Timeline: 14 months from start to certification
Months 1-2: Comprehensive gap assessment revealed only 12 of 110 practices compliant. Essentially starting from scratch. Major infrastructure replacement required.
Months 3-5: Strategic decision to move to cloud infrastructure (Microsoft 365 GCC High) rather than upgrading on-premises systems. Migration planning and execution.
Months 6-9: Implemented security controls in cloud environment, deployed MFA, configured encryption, established logging and monitoring. Cloud migration was faster than on-premises upgrade would have been but still took 4 months.
Months 10-11: Policy and documentation development, SSP creation. Hired technical writer to assist with documentation.
Months 12-13: Internal testing, staff training, readiness preparation. Discovered some gaps in access controls requiring remediation.
Month 14: C3PAO assessment. Passed with recommendations for continuous monitoring enhancements.
Key Success Factors: Strategic cloud migration decision accelerated implementation compared to on-premises approach. Investment in professional technical writing for documentation.
Challenges: Initial infrastructure assessment revealed extent of technical debt requiring replacement strategy. Budget approval for cloud migration took 6 weeks. Some manufacturing staff resistant to MFA initially.
Example 3: IT Service Provider (Northern Virginia) - Level 2
Organization: 30-person managed service provider supporting government contractors
Starting Point: Strong existing cybersecurity program, already following many NIST SP 800-171 practices
Timeline: 5 months from start to certification
Month 1: Gap assessment revealed 83 of 110 practices already compliant. Primary gaps in formal documentation and some advanced logging requirements.
Months 2-3: Enhanced logging capabilities, implemented additional access controls, deployed enhanced monitoring. Most technical implementation complete in 6 weeks.
Month 4: SSP development and documentation. Since practices were largely implemented, documentation focused on accurately describing existing implementations.
Month 5: Internal review, staff preparation, C3PAO assessment. Passed assessment on first attempt.
Key Success Factors: Strong starting position from existing security program, mature IT environment, experienced IT security staff internally.
Challenges: Despite strong implementation, documentation still required significant effort. Describing how practices are implemented is different from implementing them.
Example 4: Small Software Company - Level 1
Organization: 8-person software development company
Starting Point: Cloud-based operations, modern security practices, minimal formal policies
Timeline: 2.5 months from start to attestation
Weeks 1-2: Internal gap assessment against 17 Level 1 practices. Most technical practices implemented through cloud services, gaps in formal policies and documentation.
Weeks 3-6: Developed formal security policies covering 17 practices, documented existing implementations, established media sanitization procedures, enhanced access control documentation.
Weeks 7-8: Staff training on policies and procedures, internal compliance review.
Weeks 9-10: Self-assessment completion, attestation submission.
Key Success Factors: Small size, cloud-based infrastructure with built-in security, modern practices already in place, focused implementation effort.
Challenges: Limited internal resources meant all work fell on one person while managing other responsibilities.
Common Timeline Patterns
Across these examples and hundreds of other CMMC implementations, several patterns emerge:
Starting position matters most: Organizations with strong existing security complete 2-4 months faster than those starting from minimal security.
Documentation always takes longer than expected: Even organizations that nail technical implementation find documentation creation time-consuming.
Technology lead times add weeks: Equipment procurement, software licensing, and cloud service provisioning create delays.
Budget approval delays are common: Organizations underestimate the time required to secure approvals for CMMC expenditures.
Cloud migrations can accelerate timelines: Despite the effort of migration itself, cloud platforms with built-in security controls often result in faster overall implementation than upgrading aging on-premises infrastructure.
Small organizations move faster: Fewer systems, simpler environments, and streamlined decision-making help small organizations complete implementation more quickly than large ones (all else being equal).
Start Your CMMC Timeline Today
The timeline question isn't just "how long does CMMC take?" - it's "when do you need to start?"
If you have contracts requiring CMMC certification in 2026, and you haven't started implementation, you're likely already behind. Level 2 certification requiring 6-12 months means starting in early 2026 for late-2026 deadlines creates minimal buffer for unexpected complications.
The reality of CMMC timelines is this: organizations that start early and plan realistic schedules succeed. Those that delay until deadline pressure forces action struggle with compressed timelines, rushed implementations, and assessment failures.
Where you start matters. What resources you commit matters. How realistically you plan matters.
But when you start matters most of all.
Get Your Personalized CMMC Timeline Assessment
Every organization's CMMC timeline is unique based on current security posture, IT complexity, resource availability, and specific requirements.
CISPOINT specializes in helping defense contractors throughout Maryland, the DMV region, Huntsville, Alabama, Kentucky, and Florida navigate CMMC compliance with realistic timelines and successful outcomes.
Our CMMC Timeline Assessment provides:
- Comprehensive evaluation of your current security posture
- Analysis of your specific CMMC level requirements
- Detailed gap assessment identifying what needs to be implemented
- Realistic timeline estimate based on your starting point and resources
- Phase-by-phase implementation plan with specific milestones
- Budget requirements for successful completion
- Critical path analysis identifying potential delays
- Resource planning recommendations
As a Cyber-AB Registered Practitioner Organization (RPO), we have the expertise to accurately assess your timeline requirements and guide you through every phase from planning through successful certification.
Don't let unrealistic timeline expectations derail your CMMC compliance. Contact us today for a complimentary timeline consultation and start your journey toward certification with confidence.
Disclaimer: This guide provides general information about CMMC implementation timelines based on current DoD guidance and industry experience as of February 2026. Individual timelines vary significantly based on organizational circumstances, starting security posture, resource availability, and specific requirements. CMMC requirements and implementation schedules are subject to change as the program continues to evolve. This content should not be considered legal, compliance, or cybersecurity advice for your specific situation. Organizations should consult with qualified CMMC practitioners, legal counsel, and their contracting officers to determine their specific timeline requirements and compliance obligations. Timeline estimates provided represent typical scenarios and are not guarantees of implementation duration for any specific organization.
About the Author: CISPOINT is a Cyber-AB Registered Practitioner Organization (RPO) and Managed Security Service Provider (MSSP) specializing in CMMC compliance for defense contractors. Based in Columbia, Maryland, we serve organizations throughout the DMV region, Huntsville, Alabama, Kentucky, and Florida with comprehensive cybersecurity and compliance services.